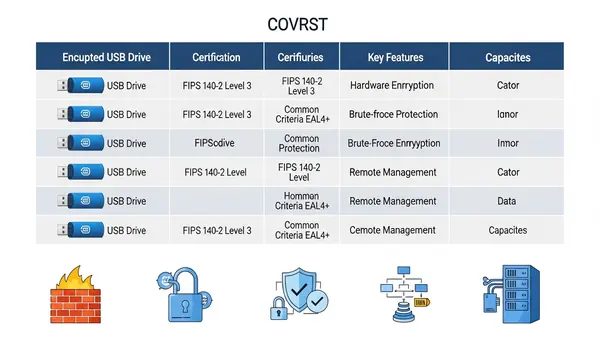
Quick Answer: The Apricorn Aegis Secure Key 3NXC is the best encrypted USB drive for most businesses in 2026, offering FIPS 140-2 Level 3 validation, hardware encryption, and onboard PIN authentication that works without software. For organizations requiring the highest security standard, the Kingston IronKey Vault Privacy 80 provides FIPS 140-3 Level 3 certification with multi-password options and remote management capabilities.
This article contains affiliate links. PacketMoat may earn a commission at no extra cost to you when you purchase through these links. This helps support our cybersecurity research and content creation.
A single lost USB drive containing customer data can trigger GDPR fines, breach notification requirements, and devastating reputation damage. Yet many businesses still rely on software-encrypted drives or worse, unencrypted storage that puts sensitive information at risk every time an employee walks out the door.
Hardware-encrypted USB drives eliminate this vulnerability by encrypting data at the controller level, independent of the host computer’s operating system. Unlike software encryption that can be bypassed through malware or OS exploits, hardware encryption keeps your data protected even if the drive is connected to a compromised machine. For businesses handling regulated data—financial records, healthcare information, customer databases—FIPS-validated hardware encryption isn’t optional anymore.
The drives in this guide meet strict criteria: FIPS 140-2 Level 3 validation minimum, hardware-based AES 256-bit encryption, brute-force protection, and enterprise-grade build quality. These aren’t consumer drives with software add-ons. They’re purpose-built security devices that comply with data protection regulations and survive real-world business use.
Apricorn Aegis Secure Key 3NXC: Best Overall for Business
The Apricorn Aegis Secure Key 3NXC delivers enterprise-grade security in a drive that actually works the way busy professionals need it to. FIPS 140-2 Level 3 validated with hardware AES-XTS 256-bit encryption, it authenticates through an onboard keypad—no software installation, no admin rights required, works on any computer including locked-down corporate machines.
The drive enforces a 7-15 digit PIN with configurable complexity requirements and locks permanently after 20 failed attempts, making brute-force attacks impractical. Its epoxy-coated electronics resist physical tampering, while the IP68 rating protects against dust and water immersion. Unlike software-encrypted drives that leave forensic traces on host computers, the Secure Key 3NXC maintains zero footprint—critical for Executive Travel Security: Why Faraday Bags Are Mandatory for Protecting Corporate Assets (2026).
Available in capacities from 8GB to 128GB with USB 3.2 Gen 1 speeds (up to 300MB/s read), it handles daily file transfers without frustration. The drive ships with a built-in Admin mode for IT departments that need to deploy multiple units with standardized security policies. At around $150-200 depending on capacity, it costs more than consumer drives but eliminates the breach risk that makes that investment trivial.
Best for: SMBs and enterprise teams that need proven security without complicated deployment. Legal firms, healthcare providers, and financial services companies that must demonstrate FIPS compliance will appreciate the validation documentation included with each drive.
Apricorn Aegis Secure Key 3NXC

Kingston IronKey Vault Privacy 80: Highest Security Standard
The Kingston IronKey Vault Privacy 80 (VP80) achieves FIPS 140-3 Level 3 certification—the newest and most rigorous cryptographic standard available in 2026. This matters for government contractors, defense suppliers, and enterprises with advanced threat models who need to meet the latest federal requirements. The VP80’s XTS-AES 256-bit hardware encryption runs on a dedicated cryptographic processor that’s physically separate from the USB controller, providing additional isolation against side-channel attacks.
Beyond raw security specs, the VP80 introduces multi-password capabilities: separate user and admin passwords, plus a one-time recovery password for emergency access. The admin mode enables centralized management through Kingston’s IronKey EMS software, allowing IT teams to enforce password policies, set maximum failed login attempts, and remotely disable lost drives. The drive’s digitally signed firmware prevents malicious firmware modifications—a sophisticated attack vector that compromised some older USB devices.
Performance reaches USB 3.2 Gen 1 speeds with read/write rates up to 250MB/s, adequate for business document transfers though not the fastest option available. The zinc casing provides physical durability with an IP57 rating for dust and water resistance. Capacities range from 16GB to 512GB, with pricing starting around $200 for the 64GB model.
Best for: Organizations with stringent compliance requirements, government contractors bound by NIST standards, and enterprises that need centralized USB drive management. The higher price point (roughly 30% more than FIPS 140-2 alternatives) buys you the most current security certification and advanced administrative features.
Kingston IronKey Vault Privacy 80

DataLocker Sentry K350: Best for Field Teams
The DataLocker Sentry K350 prioritizes durability and usability for teams working outside controlled office environments—construction managers, field service technicians, sales teams visiting client sites. Its ruggedized aluminum housing withstands 4-foot drops and carries an IP67 rating that survives dust, mud, and water submersion. The integrated keypad uses capacitive touch buttons that work reliably even when wet or with gloved hands, solving a practical problem that plagues other encrypted drives in field conditions.
FIPS 140-2 Level 3 validated hardware encryption protects data with AES 256-bit XTS mode, while the drive’s tamper-evident construction makes physical attacks obvious. The K350 includes DataLocker’s SafeConsole management platform (subscription required after first year), enabling IT administrators to track drive locations, enforce password policies, and remotely wipe devices reported lost. This cloud-based management works particularly well for distributed teams where collecting physical devices for updates isn’t practical.
USB 3.2 Gen 1 interface delivers read speeds up to 250MB/s, sufficient for transferring project files, technical drawings, and field documentation. Available in 16GB to 256GB capacities starting around $180 for the 64GB model. The drive’s rechargeable battery powers the authentication keypad independently, allowing PIN entry before connecting to any USB port—useful when working with systems that restrict USB devices until after authentication.
Best for: Field operations, construction firms, manufacturing teams, and any business where encrypted drives face harsh physical conditions. The cloud management capability makes it ideal for companies with distributed workforces who need centralized security oversight without physical device collection.

Worth Considering: Alternative Options
The iStorage datAshur PRO2 offers FIPS 140-2 Level 3 validation with a unique wear-resistant keypad coating that prevents PIN discovery through button wear patterns—a legitimate concern with frequently-used drives. Its epoxy-potted electronics and IP68 rating match the Apricorn’s protection, while read speeds reach 294MB/s. At similar pricing to the Aegis Secure Key 3NXC, it’s worth comparing if you prefer the datAshur’s specific keypad design or need the slightly faster transfer speeds. iStorage datAshur PRO2
For budget-conscious small businesses, the Apricorn Aegis Secure Key 3z provides FIPS 140-2 Level 3 encryption at roughly 30% less than the 3NXC by using USB 3.0 (rather than 3.2) and a slightly less rugged exterior. It maintains the same hardware encryption and zero-footprint operation but sacrifices some transfer speed and physical protection. Acceptable for office-based teams with lower durability requirements, though the price difference narrows enough that most businesses should invest in the 3NXC’s improved specs.
Quick Comparison Summary
For most businesses, the Apricorn Aegis Secure Key 3NXC delivers the best balance of security, usability, and value. It deploys easily, requires no software, and meets compliance requirements without complexity.
Organizations requiring FIPS 140-3 certification or advanced management features should choose the Kingston IronKey Vault Privacy 80, accepting the higher cost for the most current security standard and centralized administration.
Field teams working in harsh conditions need the DataLocker Sentry K350, where ruggedized construction and cloud management justify the investment in a drive that survives real-world abuse while maintaining security.
Final Verdict by Use Case
Professional services firms (legal, accounting, consulting) handling confidential client data should deploy the Apricorn Aegis Secure Key 3NXC across their teams—it provides proven security with simple PIN authentication that doesn’t disrupt workflows. Healthcare organizations and government contractors bound by strict compliance frameworks need the Kingston IronKey Vault Privacy 80’s FIPS 140-3 certification and audit-friendly documentation. Construction, manufacturing, and field service companies should invest in the DataLocker Sentry K350’s rugged design and cloud management that matches their operational reality.
Pair any hardware-encrypted drive with comprehensive security policies including Best Password Managers for Remote Teams (2026 Review) and Phishing-Proof Your Remote Team: Why the YubiKey 5 NFC is Mandatory for SMB Security (2026 ROI Guide) for a defense-in-depth approach. Remember: the best encrypted USB drive is worthless if employees bypass it by emailing unencrypted files or using personal cloud storage.
Frequently Asked Questions
What’s the difference between FIPS 140-2 Level 3 and FIPS 140-3 Level 3 for encrypted USB drives?
FIPS 140-3 is the newer standard released in 2019 with more rigorous testing requirements, particularly around physical security and firmware integrity. Both levels provide strong encryption, but FIPS 140-3 validation demonstrates compliance with the most current federal standards—critical for government contractors and organizations with advanced security requirements. For most SMBs, FIPS 140-2 Level 3 remains sufficient and widely accepted for compliance purposes.
Do encrypted USB drives work with Mac, Linux, and locked-down corporate computers?
Hardware-encrypted drives with onboard keypads (like all our top picks) work across all operating systems without installing software or requiring admin rights. You authenticate via the keypad before connecting, and the drive appears as standard USB storage once unlocked. This makes them ideal for executive-travel-security-faraday-bags where you may need to access files on unfamiliar systems or heavily restricted corporate networks.
Can IT departments remotely wipe encrypted USB drives if an employee loses one?
Only drives with management software support remote wiping—the Kingston IronKey Vault Privacy 80 (via IronKey EMS) and DataLocker Sentry K350 (via SafeConsole) offer this capability. Drives without management platforms like the Apricorn Aegis Secure Key 3NXC rely on brute-force protection that permanently locks the drive after failed PIN attempts, effectively rendering data inaccessible but not actively wiping it. Choose based on whether you need active remote management or accept the security of automatic lockout.
Are hardware-encrypted USB drives slower than regular USB drives?
Modern hardware-encrypted drives perform nearly identically to standard USB 3.2 drives for everyday business use. The encryption happens at the controller level with dedicated processors, creating minimal performance impact. Our recommended drives achieve 250-300MB/s read speeds—sufficient for transferring large presentations, databases, and document archives without noticeable delays compared to unencrypted alternatives.
What happens if I forget my PIN on a hardware-encrypted USB drive?
Most hardware-encrypted drives permanently lock and erase all data after a set number of failed PIN attempts (typically 10-20 tries) with no recovery option—this is a security feature, not a bug. Some enterprise models like the Kingston IronKey Vault Privacy 80 offer admin recovery passwords set during initial configuration, but this requires planning ahead. The lesson: treat your PIN like you would treat the actual data on the drive, and consider using a best-password-managers-remote-teams to securely store drive PINs for business-critical devices.